z/OS Security Blind Spots: What Best Practice Guides Are Missing About Your PROCLIBs
Let’s be honest: in the Z operating system world, we often get obsessed with the "usual suspects." Ask any auditor or security pro what they check first to lock down an LPAR, and they’ll recite the sacred list: APF-authorized libraries, the Linklist, and critical volume protection. Don’t get me wrong—meeting these standards is vital for ISO 27001 or PCI DSS compliance. But for those of us who have spent years developing ethical hacking techniques specifically for z/OS, we know that’s simply not enough.
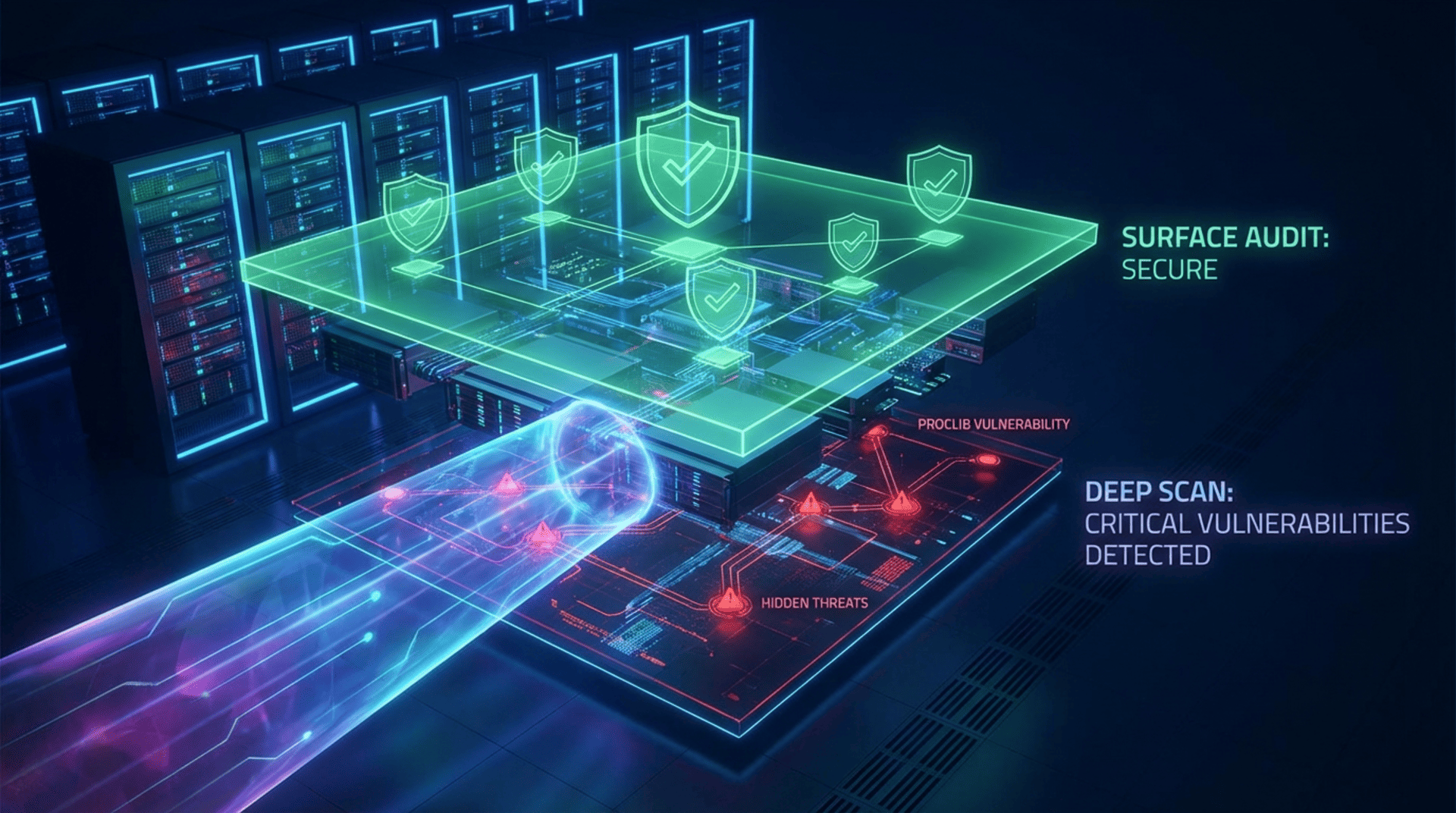
The real problem lies in the lack of awareness regarding "silent" attack vectors. There is a false sense of security when you see all green checks on a standard Sarbanes-Oxley compliance audit or a PCI certification report.
The Architecture’s Achilles Heel
I’ve seen it too many times: the focus remains on the obvious PCI 12 requirements, while libraries that seem harmless—like PROCLIB, SYSPROC, or other operational datasets—are left exposed. Their strategic importance for system robustness is often hidden from the untrained eye, yet they are gold mines for penetration testing. The operational reality is stubborn. On multiple occasions during ethical hacking engagements, we have successfully exploited privilege escalation simply because a PROCLIB library lacked adequate protection. The technique is as old as it is effective: we modify a member in a procedure library used by a Trusted STC (Started Task) or a privileged task, and then we wait. When that STC starts, the system installs a backdoor for us. Quietly. Without triggering alarms if your monitoring doesn’t go beyond basic PCI data security standard checks. This proves an uncomfortable truth: control verification guides, like the DISA STIGs or CIS benchmarks, while reasonable and necessary, are not perfect. They are static snapshots that often fail to capture the dynamic logic of an orchestrated attack.The Impact on Regulatory Compliance (DORA, NIS2, and GDPR)
This is where the CISO’s role becomes critical. We aren’t just talking about a technical glitch; we are talking about business survival and legal mandates. With the Digital Operational Resilience Act 2022 (DORA) and the NIS2 directive now in effect, digital operational resilience is mandatory. A privilege escalation attack on the mainframe that compromises sensitive data puts you on a direct collision course with GDPR, PCI, and alignment with both. What good is it to have a SOC monitoring the perimeter or worrying about Solvency II compliance if the heart of the business—the mainframe—has open doors from the inside?Integrating Mainframe into Modern Cybersecurity
To mitigate this, passing the annual ISO 27001 certification cost analysis isn’t enough. We need:- Real Visibility: You need to go beyond basic PCI DSS 12 requirements. You must integrate z/OS logs into a corporate SIEM.
- Recurring Ethical Hacking: Move beyond simple vulnerability scanning. You need to test PROCLIB and SYSPROC configurations with an attacker’s mindset, not just a compliance audit checklist.
- Education: Understand z/OS in the context of modern threats. It’s not an isolated black box; it’s a critical node that must comply with Sarbanes-Oxley standards, Basel III, and the strictest payment card industry regulations.