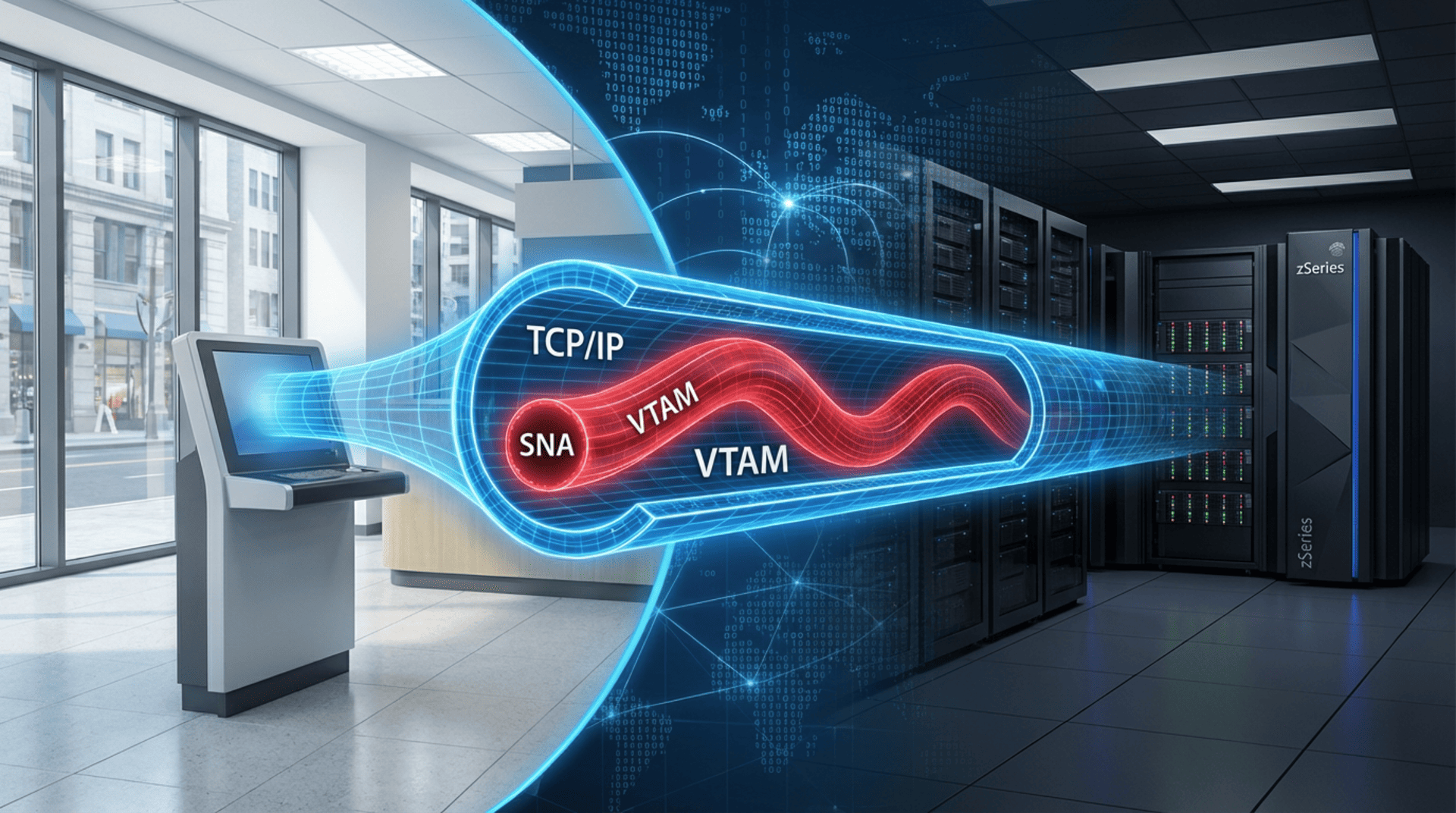
We often live with a false sense of security, believing that the old SNA (Systems Network Architecture) protocol is a relic of the past, completely displaced by the ubiquitous TCP/IP. But the reality in z operating system (z/OS) environments is much more stubborn: SNA hasn't disappeared; it has simply gone into hiding.
There is a hidden problem, almost invisible to most CISOs and security managers, related to the progressive—but never complete—abandonment of the old SNA/VTAM. Today, there is still a massive amount of communication to and from mainframe applications using legacy protocols such as LU 6.2 or 3270.
The problem? These protocols, designed in a different era, are overly trusting: they don’t authenticate the identity of the person they're talking to. And this is where the door swings wide open for attacks like "Man in the Middle."
The Real Story: The "Hack" from the Branch Office
To prove this isn't science fiction, let me share a real case we documented. It’s a story that would keep any risk manager awake at night. It happened at a financial institution, with an employee working in a business branch thousands of miles away from the data center hosting the mainframe serving the data.
This employee, with some technical knowledge but no privileged credentials—perhaps someone who had taken an ethical hacking course but used it for the wrong reasons—managed to achieve a disturbing feat: capturing the passwords of a large number of users, including system administrators. Once he had the keys to the kingdom, he logged in as them and installed software that left "backdoors" open.
How did he do it?
The technique was as brilliant as it was dangerous. He booted up a Hercules emulation on his office computer and requested a connection to the bank's production TSO system.
This is where the skeptics usually interrupt: "But what about the firewall? What about perimeter security?" The bank had spent a fortune on security software, next-generation firewalls, and had a SOC monitoring 24/7. They were worried about PCI DSS firewall requirements and the cost of ISO 27001 certification for company compliance, yet all this was useless against this specific vector.
The connection between the office and the mainframe indeed traveled over TCP/IP. But—and here is the kicker—every IP packet contained the SNA protocol. The firewalls, diligent as they were, verified that the request came from a correct IP and MAC address at the branch. They gave the green light. But they were unable to inspect the payload: the VTAM commands inside walked right through the front door and executed in their native environment.
The Invisible Attack
Once the attacker established a session between his Hercules emulator and the production LPAR via SNA, he simulated the system's logon screens. When a legitimate user tried to log in, the attacker captured their username and password, displayed a fake connection error, and immediately switched to transparent mode, allowing the real traffic to pass through. The user thought they had made a typo, tried again, and got in. But their credentials had already been stolen.
When the attacker harvested credentials from users with enough power, he waited for hours until he knew these administrators weren't working to connect with impunity.
The Blind Spot in Compliance: From PCI DSS to DORA
This scenario raises an uncomfortable question: What is the point of a SIEM if it cannot see what is happening inside this SNA tunnel?
In the current regulatory landscape, full visibility is non-negotiable. It is no longer enough to just worry about the Payment Card Industry Data Security Standard (PCI DSS) or having an ISO 27001 certificate on the wall.
Whether you are dealing with Sarbanes-Oxley compliance audit requirements, Basel III (or Basel 3) standards for risk, or the new Digital Operational Resilience Act 2022 (DORA), you cannot afford blind spots. If your security team is focused on NIS 2 compliance or meeting PCI DSS 12 requirements, ignoring this legacy traffic is a critical failure.
Think about it: SOX regulatory requirements and Solvency II data quality standards demand strict internal controls. If your SIEM doesn't receive data on what happens within the guts of the VTAM protocol, you are failing the basic principle of security monitoring. You are blind to traffic that remains vital to your business.
DataPASS: Turning on the Light in the Darkness
This vulnerability still exists in any application using old encapsulated VTAM protocols—something much more common than most admit. The question I put to you is: How many applications are still connecting with these protocols in your installation? Have you ever checked, or are you one of those who defend to the death that "we only use TCP/IP here"?
To fix this security hole, it is necessary to increase the frequency and depth of cyclical audit services. This is where our DataPASS system comes into play, designed for the continuous improvement of mainframe security.
DataPASS has a specific component that can generate SMF (System Management Facilities) records for all VTAM activities. We transform what was once an inscrutable "black box" into clear, structured data.
Thanks to this, we can analyze all connections, traffic, users, and applications, and inject that information directly into your SIEM or analyze it later in the DataPASS daily cycle.
In this way, we convert a hidden risk and a potential breach of regulations such as GDPR, DORA, NIS2, or the Payment Card Industry Data Security Standard into a controlled, auditable, and secure environment. Don't let old SNA be the backdoor through which they sneak into your organization.